WSO2 API Management: Permissions Model, Authorization, Analytics and API Life Cycle
API Management Solutions are elements of a mature integration architecture. They provide API management functionalities for all interested parties (developers, administrators, consumers). In this article, I will briefly present a solution that we use for this purpose in Unity – WSO2 API Manager.
API Management and approaches to it
First, I’ll present how API management is defined and the elements comprising it:
- sharing the API catalog – a place (website) where the API can be viewed, checked, evaluated, etc.,
- API life cycle management – creating, prototyping, publishing or disabling the API,
- load-balancing,
- API access limitation – determining who and on what terms will have access to specific resources,
- monitoring and analytical dashboards showing e.g. statistics on the use of the API,
- API security (authentication and authorization).
Of course, these functionalities can also be implemented in a different way using certain programming frameworks/libraries (e.g. Spring Boot, Swagger) or additional tools (e.g. Nginx, Prometheus). By using these types of elements, most of the basic functionalities can be implemented with little effort. Using the (example) tools/frameworks usually does not require the acquisition of additional knowledge by programmers or DevOps teams (as a rule, they are still used for other purposes).
Each of the approaches (dedicated API Management solution and programming tools/frameworks) has its specific features. The advantages of API Management are evident when you look at the API from the perspective of the entire organization. Then it becomes important that our APIs are shared, monitored and secured in a uniform and fast way. In addition, API Management solutions, dedicated to this purpose, provide several advanced functions. Their implementation is no trivial matter. If we add to this the constantly growing popularity of API, as well as the extension of selected API Management solutions, it comes as no surprise that they make up an increasingly frequent element of IT architecture in organizations.
API Management solutions are used both to publish APIs within an organization (in local networks) and to make them publicly available on the Internet. Publishing an API outside the organization is perfectly understandable, not only due to the automation of data exchange with partners but also to such concepts as commercialization (monetization) of the API. However, internal APIs are equally important. They are used by cooperating development teams, and work can be accelerated when there is a unified mode and place for sharing them. This is of increasing significance because of the growing importance and popularity of microservice architectures.
WSO2 API Management characteristics
A full description of the solution can be found on the product’s website. In this section I’ll briefly present its characteristics, with attention paid to the most important and most interesting issues.
API Management and role and permissions model
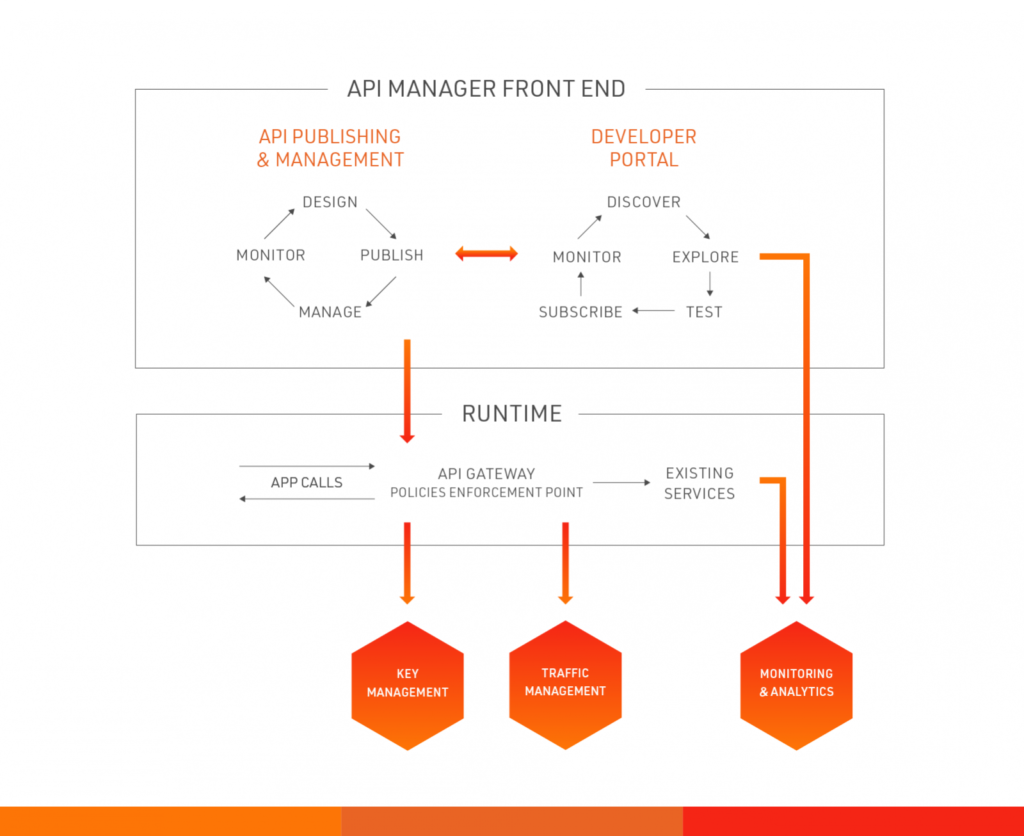
WSO2 API Management provides 4 basic consoles (websites) enabling the execution of individual operations:
- / carbon – a management console that allows you to add and modify roles and users, configure the Manager API and monitor technical metrics (e.g. from JVM),
- / publisher – a console that allows you to publish the API and view basic statistical data,
- / admin – a console that allows you to configure elements related to published APIs (e.g. custom access restrictions, alerts),
- / store – console presenting published API (endpoints, swagger console enabling testing, documentation, SDK) and allowing to subscribe to them.
The role and authorization model is quite extensive and allows you to create roles (and assign users to them) entitling you to selected actions (about 100 different rights). This means you can create separate roles to view statistics, publish APIs, manage the server, use the API, etc.
Authorization/limitation of API access
Access to the API is secured at many levels. The first of these is authorization, which is most often implemented (in production solutions) through OAuth2 or SAML tokens. There are more possibilities, and details can be found on product’s website. Using OAuth2 scopes also allows you to block access to selected methods of a given API.
One element that should be given consideration in this respect is limitation or throttling. It allows you to limit requests sent to the API. These restrictions may apply to both the number of requests and the size of the data sent from/to the API (e.g. in KB). The entire API may be subject to limitation or only its selected methods (e.g. to protect the backend system against excessive loads). You can also limit access for selected users (e.g. by subscription level). The ability to set limits at many levels gives you great flexibility in terms of protection against excessive use of the API.
Analytics
API statistics are available by default – however, they require the installation of a dedicated module (API Management Analytics or Analytics & Stream Processing). Basic charts show information such as the number of requests sent to the API by individual clients over time, the number of unsuccessful queries, published APIs, and subscribed users.
An additional option is to use a dedicated portal that allows you to prepare dedicated dashboards and charts for individual users. It should be mentioned here that the analytical module is based on a stream processing. This allows full freedom in what happens to analytical data published to streams. In the simplest case, they can be saved to an external database and further “processed” using other analytical tools (e.g. Power BI). In a more complicated scenario, you can search for streams of certain anomalies and prepare an alert mechanism (e.g. e-mail) regarding, for example, capture of unwanted use of the API.
API life cycle
The API life cycle is particularly important when it is used by many clients. Any change to the API can affect and force a modification on the side of client systems and applications. Therefore, whenever you modify the API, you should consider whether it should be done through alteration or, for example, by releasing a new version. Similarly, depreciation, blocking and disabling the API should always be done with caution. WSO2 API Management supports API life cycle management at all the stages mentioned above.

Summary
In the face of progressing digitization and integration of IT solutions, as well as changing approaches to software construction (microservices), the importance of API is constantly growing. Appropriate API management is therefore extremely important. One of the ways to handle this task is an API Management solution that enables uniform sharing, securing and monitoring of the API. WSO2 API Management stands out in this class of solutions which, in addition to its complete and expandable set of functionalities, is fully available under an open-source license.








